For cloud customers looking to meet security compliance requirements, AWS GovCloud often seems like a good option. At Oxalis, we frequently help customers deploy their workloads in AWS GovCloud to meet their compliance needs – we even wrote the User Guide to AWS GovCloud!
Limited to just US customers, AWS GovCloud is, as Amazon puts it, “… designed to address specific regulatory and compliance requirements of US government agencies at the federal, state, and local level, as well as contractors, educational institutions, and other U.S. customers that run sensitive workloads in the cloud.”
After helping customers with compliant cloud migrations and deployments for many years, similar questions kept coming up. In this post we share 5 key concepts that customers should take into account when considering a migration to AWS GovCloud.
You May Not Need AWS GovCloud
Many people hear about GovCloud and assume that because they have compliance requirements, they must use GovCloud. Depending on the specific compliance regime however, you may be able to use AWS’s standard Commercial offerings.
For instance, for customers requiring FedRAMP Moderate compliance, AWS’s standard US East and West regions are compliant and have an ATO.
AWS US East-West (Northern Virginia, Ohio, Oregon, Northern California) has been granted a Joint Authorization Board Provisional Authority-To- Operate (JAB P-ATO) and multiple Agency Authorizations (A-ATO) for moderate impact level. The services in scope of the AWS US East-West JAB P-ATO boundary at Moderate baseline security categorization can be found within AWS Services in Scope by Compliance Program.
https://aws.amazon.com/compliance/fedramp/
AWS’s Compliance program is a good starting point for understanding what compliance regimes exist and if GovCloud is required to meet them. https://aws.amazon.com/compliance/services-in-scope/
At Oxalis, our first question on any compliant cloud project is what specific compliance regimes need to be covered. Choosing GovCloud unnecessarily can add cost and complexity if its unique certifications are not required.
Unsure if AWS GovCloud is the right choice for your compliance needs?
AWS GovCloud Has Different Services and Features
GovCloud is not “just another region” – new AWS services can take years to be made available as they go through the certification process. For instance, AWS ChatBot, a tool for Slack and Teams integrations, is not available in AWS GovCloud.
This means that if your solution depends on a specific AWS service, it is important to review the services currently in govcloud to avoid surprises – https://aws.amazon.com/govcloud-us/details/
While understanding whole services that are/are-not available is a relatively straightforward process, far more challenging is when specific services are missing features in GovCloud. For instance, while AWS Lambda is available in GovCloud, using a Container Image for a function is NOT. Almost every service has similar caveats that can cause surprises in GovCloud deployments.
Unlike services, there is no master list of these differences and sometimes aren’t documented at all. Successful, predicable GovCloud implementations require teams with GovCloud specific experience, not just AWS in general.
Looking for a GovCloud experienced team to help with an implementation?
Just Because a Service is in GovCloud doesn’t mean it is certified
Because AWS GovCloud can be used to meet many different compliance requirements, if a specific service is available within GovCloud does not mean it has been certified. For Instance, AWS Firewall Manager is available in GovCloud but does not yet have approval for FedRAMP High. It is under review so it will likely be certified, but at time of writing you cannot use AWS Firewall Manager for FedRAMP high offerings.
Every GovCloud Account has a corresponding Commercial Account
As documented in our User guide, GovCloud accounts get created from a “standard” AWS account, with the standard account continuing to manage billing and budget management. For basic cloud deployments, this is as far as the account structure goes. If, however, you’re trying to setup a multi-account architecture following their recommendations for a well architected environment (https://docs.aws.amazon.com/whitepapers/latest/organizing-your-aws-environment/organizing-your-aws-environment.html) or the Compliant Framework for Federal and DoD Workloads in AWS GovCloud (US), you end up with many accounts.\

In these situations, the account pairing requires a strategy to make sure that the commercial standard accounts are secured and managed to avoid risks to the GovCloud accounts
Interested in pursuing a multi-account strategy in AWS?
Security and Compliance Responsibility is Shared
There is no phrase that causes security experts to see red than “We’re secure because we’re hosted in AWS GovCloud”. Your choice of host only covers part of security needs – e.g. securing physical access to resources – but doesn’t in itself confer any compliance status.
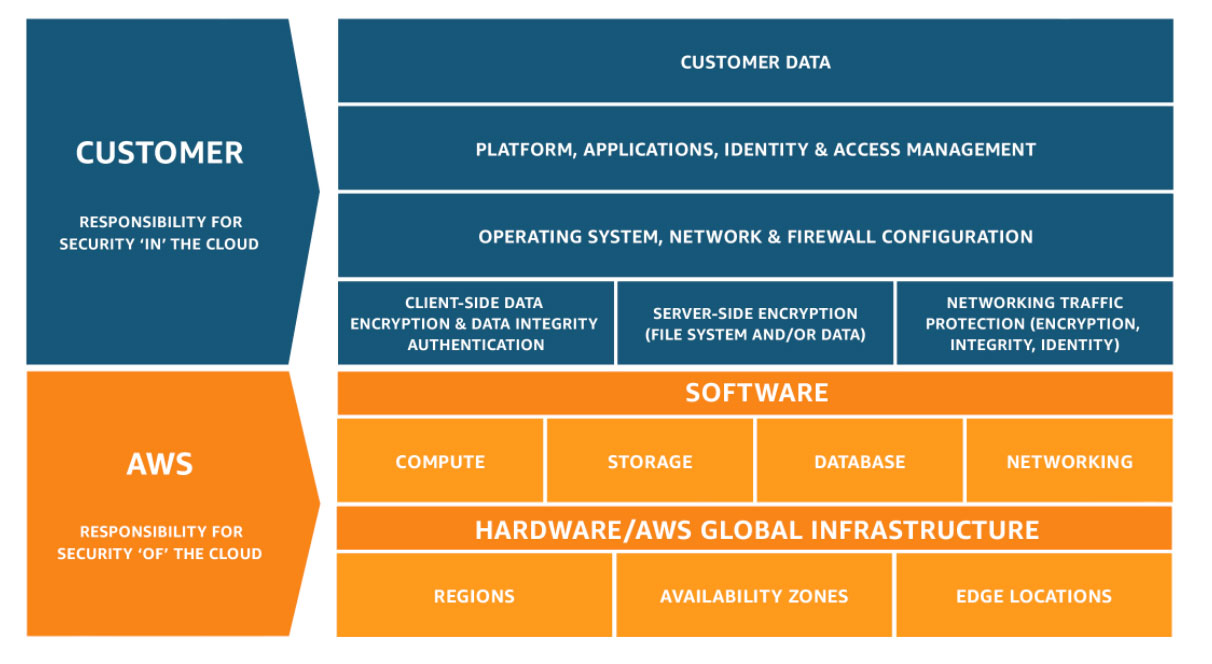
You are still responsible, for instance, for using the services in a secure manner – e.g. GovCloud will do nothing to prevent you from inadvertently making a S3 Bucket’s contents public.
Additionally, most security and compliance certifications go beyond pure technical details. Under CMMC and NIST 800-171, there is a requirement to provide employees with insider threat training. Hosting on GovCloud provides no assistance to meeting that need.
Looking for help designing your security controls?
Need more Info? Check out our AWS GovCloud Services User Guide
Here is what our AWS GovCloud user guide includes:

Bonus: Azure Government has (mostly) the same caveats
Remember, GovCloud isn’t the only option for high-compliance cloud services – Azure Government provides similar capabilities with similar caveats around service and feature availability.